The sophisticated nature of modern cyberattacks has demonstrated that securing source code alone is no longer sufficient when the very identities of those writing it are under constant siege from external threats. As organizations move deeper into a decentralized development model, the traditional perimeter has effectively vanished, leaving developer credentials as the primary target for malicious actors looking to compromise software supply chains. BlueFlag Security has emerged as a critical player in this specialized niche, having recently secured twenty-eight million dollars in Series A funding to expand its reach. This investment round, led by Maverick Ventures and Ten Eleven Ventures, follows a period of rapid expansion characterized by a three-hundred percent increase in year-over-year revenue. The company has also managed to quintuple its footprint among Fortune 500 organizations, underscoring a significant market appetite for identity-centric security measures within the software development lifecycle. By focusing on the human and machine elements rather than just the raw output of code, the platform aims to close a persistent gap in corporate defenses that legacy tools have historically ignored.
The Evolution of Software Development Security: A Shift Toward Identity
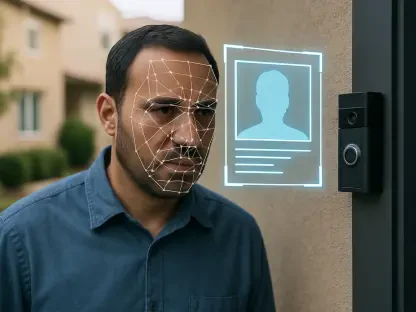
Investment in the cybersecurity sector has recently pivoted toward protecting the specialized environments where digital infrastructure is born, reflecting a broader recognition of systemic vulnerabilities. The injection of capital into BlueFlag signifies a transition from static code analysis to a more dynamic, identity-focused methodology that tracks how developers interact with their environments. Industry data suggests that a staggering seventy-five percent of risks within the development lifecycle are currently invisible to standard application security scanners. This invisibility stems from the fact that most tools look for vulnerabilities in the lines of code rather than analyzing whether the person or bot accessing the repository should be there in the first place. With approximately sixty-eight percent of data breaches now involving compromised credentials, the ability to verify the legitimacy of every action within the development pipeline has become a non-negotiable requirement for modern enterprises. Consequently, the industry is witnessing a surge in demand for platforms that can correlate identity data with behavioral patterns to prevent unauthorized access.
Building on this foundation, the integration of security directly into the developer workflow ensures that protection does not come at the expense of productivity. Traditional security measures often created friction, leading developers to find workarounds that inadvertently introduced even more risk into the system. BlueFlag addresses this by providing a unified view of the development ecosystem, allowing security teams to monitor permissions and access levels across various tools without disrupting the creative process. This approach is particularly relevant as companies scale their engineering departments and struggle to maintain oversight of who has access to which critical repositories. The platform acts as a central intelligence layer, identifying over-privileged accounts and stale permissions that could be exploited by an attacker. By focusing on these hidden risks, organizations can move from a reactive posture to a proactive one, ensuring that the integrity of the development process remains intact even as the volume of code produced continues to accelerate across global teams and diverse operating environments.
Governing the Rise of Autonomous Development: AI Agents and Behavioral Risks
As the use of artificial intelligence in software engineering becomes standard, the introduction of AI Agent Governance has become a cornerstone of the modern security strategy. Tools such as Copilot and Cursor are no longer just optional assistants; they are increasingly responsible for writing and deploying significant portions of the codebase without direct human intervention. This shift has introduced a new class of “machine identities” that require the same level of scrutiny as human developers to ensure they do not introduce malicious vulnerabilities or excessive permissions. BlueFlag’s governance framework provides a structured way to manage these autonomous entities by establishing behavioral baselines and rigorous audit trails. By monitoring for anomalies, such as an AI agent suddenly requesting access to sensitive data stores or cloning an unusual number of repositories, the system can flag potential takeovers before damage occurs. This level of oversight is essential for maintaining trust in automated systems that are quickly becoming a permanent fixture in the competitive landscape of software creation.
The implementation of advanced behavioral risk analysis further strengthens the defense by identifying patterns that deviate from established norms for any given identity. For instance, if a developer who typically works on front-end components suddenly begins accessing core security modules during off-hours, the platform can automatically trigger an investigation or restrict access. This focus on behavior rather than just static credentials helps to mitigate the impact of account takeovers, which are often difficult to detect using traditional methods. Looking ahead, the expansion of these capabilities into the US and EMEA markets will likely set a new standard for how highly regulated industries manage their development pipelines. Organizations are encouraged to transition toward a model where identity intelligence is the primary filter for all development activities. By prioritizing the governance of both human and AI actors, the industry moved toward a more resilient future where innovation is protected by design. These strategic steps ensured that as the software supply chain grew more complex, the fundamental identities at its core remained verified, monitored, and thoroughly secured.