The fundamental architecture of the corporate workspace has shifted dramatically from localized, hardware-bound software toward an expansive ecosystem of web-based applications and artificial intelligence integrations. In this decentralized environment, the web browser has emerged as the definitive operating system for modern business, serving as the primary conduit for Software-as-a-Service platforms, collaborative hubs, and generative computing. This transition has occurred with such velocity that traditional security protocols have struggled to maintain relevance, resulting in a dangerous visibility gap that leaves sensitive corporate data exposed. Statistics indicate that nearly ninety-five percent of organizations have encountered a security incident originating from a web session over the previous year, highlighting the browser as the new front line of cyber warfare. As attackers pivot their focus toward these vulnerable web sessions, executive leadership must recognize that the perimeter has evolved far beyond the network firewall into the individual tabs of an employee’s workspace.
Bridging the Divide: Legacy Security and Modern Workflows
The disconnect between legacy security frameworks and current operational realities represents one of the most significant challenges for contemporary cybersecurity teams. Many of the tools currently in place were designed for an era of physical offices and corporate-managed devices where the network perimeter was clearly defined and easily monitored. However, these traditional systems frequently fail to inspect encrypted web traffic or provide granular control over how data is manipulated within a browser environment. This lack of visibility at the final point of digital interaction creates a massive governance vacuum where critical business information moves freely between sanctioned and unsanctioned platforms. Consequently, enterprise leaders are finding that their existing security investments are increasingly ill-equipped to prevent data exfiltration or manage the complexities of hybrid work. Bridging this gap requires a fundamental rethink of how protection is applied, moving security away from the network core and closer to the actual point of execution where modern employees perform their daily tasks.
This transition toward a browser-centric model has fundamentally altered the threat landscape by moving the point of vulnerability to the individual user session. When work is performed exclusively within a web interface, traditional network-based defenses become secondary to the security of the browser itself, which acts as the ultimate gatekeeper for corporate assets. Without specific controls at this “last mile,” organizations lose the ability to track how users interact with sensitive information or identify when data is being moved into unmanaged environments. The inability to distinguish between benign browsing and high-risk activity often forces security teams into a binary choice between total restriction and excessive permissiveness. This situation is unsustainable in a competitive landscape where speed and flexibility are paramount for operational success. Leaders must therefore prioritize solutions that provide deep insight into web-based workflows without degrading the user experience or performance. Establishing a robust security posture in this new reality demands a strategy that accounts for the fluid nature of web sessions and the high volume of data that moves through them.
Navigating the Risks: Intellectual Property and Personal Devices
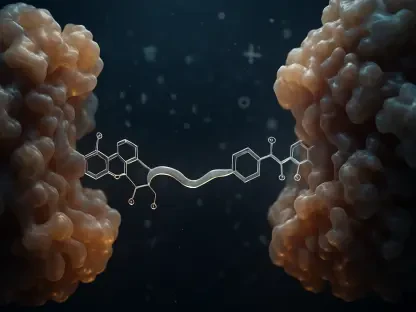
Managing intellectual property has become exceptionally complex with the integration of generative artificial intelligence into the standard professional toolkit. While these tools offer transformative productivity gains, they simultaneously introduce the risk of “shadow AI,” where employees use unsanctioned applications to process sensitive corporate data. The primary threat often stems from thousands of small, well-intentioned decisions where proprietary code, internal strategy documents, or customer details are entered into public prompts to save time or improve output. Because legacy security tools lack the context to monitor these specific interactions within the browser, they cannot prevent sensitive information from being ingested by external models. This cumulative data exposure creates a long-term risk where a company’s most valuable intellectual property could inadvertently become part of a public dataset. To mitigate this risk without stifling innovation, organizations require a governance model that provides real-time oversight of AI interactions, allowing for the safe adoption of advanced technologies while strictly enforcing data privacy boundaries.
The shift to a hybrid work model has also elevated the risks associated with unmanaged personal devices, which have become a major entry point for sophisticated cyber threats. In many modern organizations, contractors, partners, and even full-time employees utilize personal laptops or tablets to access corporate SaaS platforms, bypassing the rigorous security configurations of managed hardware. These unmanaged endpoints frequently lack updated antivirus software and may be infected with dormant malware or malicious browser extensions that are invisible to the corporate IT department. Data suggests that a vast majority of successful ransomware attacks now utilize these personal devices as a bridge to enter the broader enterprise network. For executive leadership, this represents an invisible pipeline for data exfiltration and network infiltration that traditional Virtual Private Networks or firewalls are unable to stop. Securing these endpoints is no longer just an IT requirement but a strategic necessity to protect the organization from catastrophic financial and reputational damage caused by external breaches originating in unmanaged home environments.
Countering Evasion: Browser-Native Attacks and Agentic AI
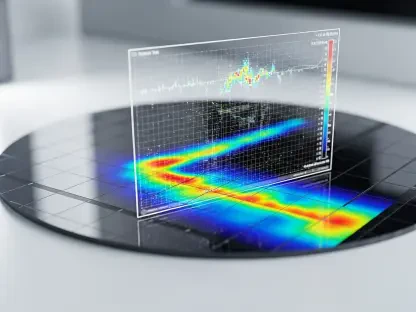
As attackers become more sophisticated, they are increasingly deploying browser-native threats that are designed to evade detection by conventional security software. One particularly effective technique is the reassembly attack, where malicious payloads are broken into small, benign-looking fragments that pass through firewalls without triggering any alarms. These pieces only reconstruct themselves into a functional threat within the browser’s local memory, making the attack invisible to standard network logs and endpoint detection systems. Furthermore, the proliferation of malicious browser extensions has added a new layer of risk, as these tools can hijack session tokens and capture sensitive credentials in real-time. When these methods are combined with AI-generated phishing lures that are virtually indistinguishable from authentic corporate communications, the result is a threat environment where human error is easily exploited. Organizations must adapt by implementing defensive layers that can analyze the behavior of web pages and extensions in real-time, identifying malicious patterns before they can execute and cause damage.
The evolution of artificial intelligence is moving beyond interactive chatbots toward agentic browsers, where AI agents can take autonomous actions on behalf of a human user. This development introduces a significant governance challenge, as these agents may inadvertently expose authentication data or perform unauthorized tasks if they are manipulated by malicious actors. Prompt injection attacks represent a critical vulnerability in this area, where hidden commands on a website can “jailbreak” an AI agent and force it to exfiltrate data or bypass security protocols. This shift creates a crisis of accountability within the enterprise, as it becomes increasingly difficult to determine whether a specific action was initiated by an authorized employee or an autonomous script acting under duress. Without clear visibility and control over these agent-driven workflows, organizations face a future where automated systems could cause widespread damage without any human intervention. Managing this transition requires new oversight mechanisms that can verify the intent of AI-driven actions and ensure that every automated process adheres to strict corporate security policies.
Strategic Integration: Specialized Browsers as Security Anchors
To address these multifaceted challenges, organizations are increasingly adopting specialized enterprise browsers that integrate security directly into the web-rendering engine. By moving the security layer to the point where data is processed and displayed, these platforms can implement content-aware and context-aware policies that are far more effective than traditional network filters. This allows a company to adopt a “controlled yes” approach toward emerging technologies like generative AI, where sensitive information is automatically identified and masked before it ever leaves the local environment. For example, a dedicated enterprise browser can distinguish between a secure internal AI environment and a public large language model, enforcing different data handling rules for each. This granular level of control ensures that employees can remain productive and innovative while the organization maintains a rigorous defense against accidental data leakage. By embedding protection within the browser interface, companies can restore the visibility and governance that were lost during the migration to a decentralized, web-centric operational model.
Dedicated enterprise browsers also provide a robust solution for the security risks posed by unmanaged personal devices and external contractors. By creating a secure, isolated workspace that can be deployed on any piece of hardware, these platforms eliminate the need for costly and complex Virtual Desktop Infrastructures or the logistical burden of shipping corporate laptops. This containerized approach ensures that even if an underlying personal device is compromised by malware or risky third-party applications, the corporate data remains protected within a secure environment. The browser can proactively scan every web page in real-time before it loads, neutralizing evasive threats like reassembly attacks and malicious scripts at the source. Additionally, by monitoring browser extensions for unauthorized updates or permission changes, these platforms close a critical blind spot that has long been exploited by cybercriminals. This holistic approach to browser security allows organizations to enable flexible work arrangements without sacrificing the integrity of their data or the stability of their broader technological infrastructure.
Future-Proofing the Enterprise: Actionable Governance Strategies
The findings of recent security audits and the rapid expansion of AI-driven workflows indicated that the browser has become the central pillar of the modern corporate infrastructure. It was determined that traditional network security measures were no longer sufficient to protect against the sophisticated, browser-native threats that emerged as employees migrated toward decentralized work models. To maintain operational resilience, leadership transitioned from broad-spectrum blocking toward more nuanced, context-aware governance strategies that favored visibility at the point of interaction. Organizations successfully mitigated the risks of shadow AI and unmanaged devices by implementing dedicated enterprise security layers that prioritized data integrity without hindering user productivity. Moving forward, the focus shifted toward establishing clear guardrails for autonomous agents and ensuring that security evolved at the same pace as technological innovation. By embracing specialized browser solutions, enterprises converted a potential point of failure into a secure, high-performance workspace that protected intellectual property while enabling the next generation of digital transformation across the global professional landscape.